Top Data Breaches of 2021
by Carmella Arroyo on Nov 29, 2021 12:00:00 AM
Everyday, the cybersecurity industry is working hard to fight against hackers who cause data breaches and ransomware attacks. But those hackers show no sign of slowing down their attacks either.
All over the world, these hackers continue to find weaknesses and vulnerabilities in all different types of organizations. In contrast to the biggest breaches of 2020, these hackers put a focus on government and healthcare organizations in 2021. They demanded millions of dollars in payment, threatening to leak private and important information from their compromised databases.
To help close out 2021, we put together some of the top data breaches that happened this year.
Twitch - 5 Billion Records Leaked
Twitch, a popular Amazon owned streaming service, confirmed that they suffered from a data breach in October this year. The leak included details from the millions earned online from popular streamers and Twitch’s entire source code. The data was posted anonymously onto the message-board site, 4chan, and included 125 gigabytes worth of data. Thankfully, user logins, passwords and other important information was not exposed. It is believed that this leak was caused by a “human error” when configuring a server and created a vulnerability in the system.
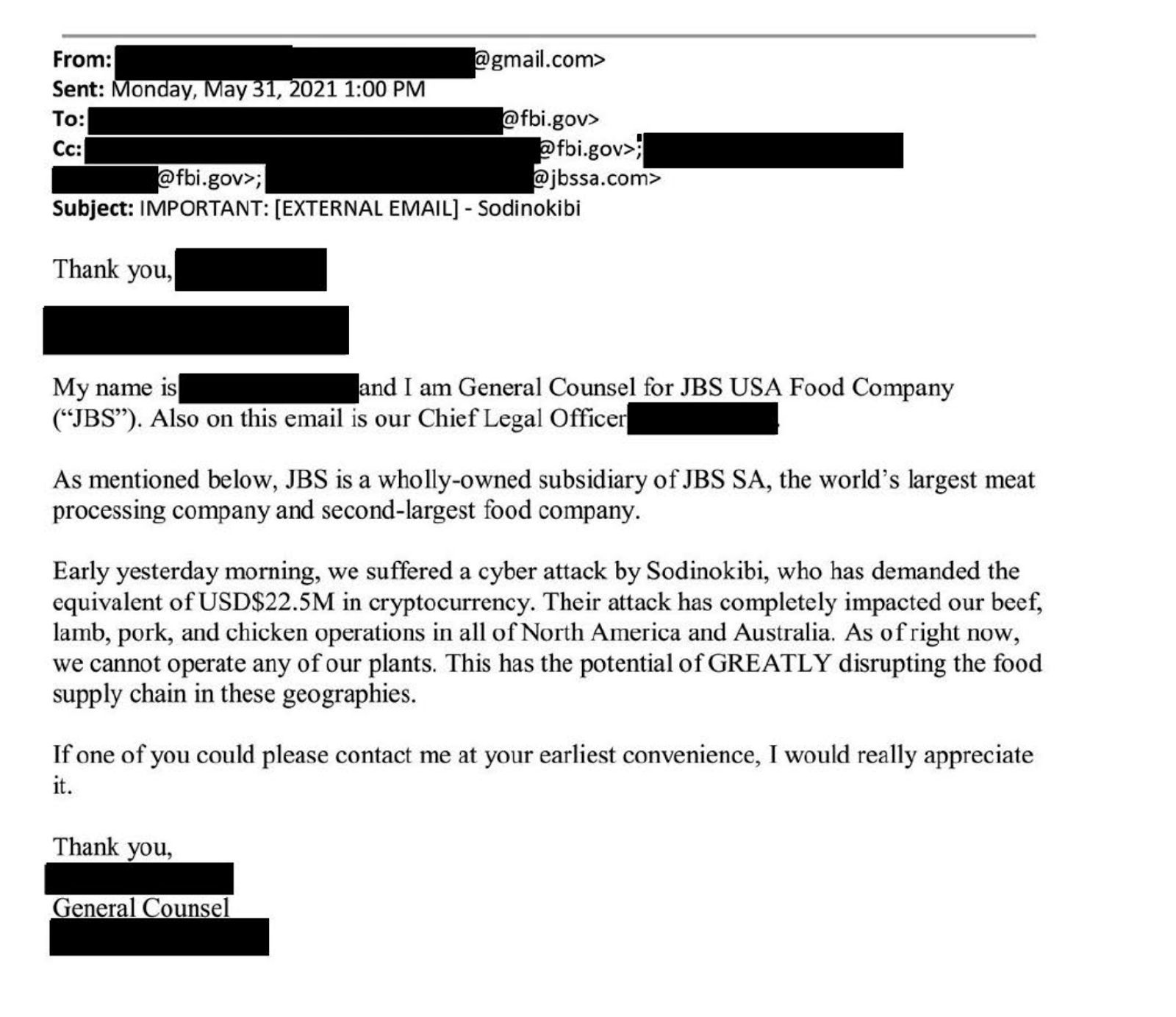
JBS Foods - $11 Million in Ransom
JBS Foods is one the largest meat processing companies in the world. In May, they were attacked by the russian hacking group, REvil. Fortunately, this attack did not lead to any big food shortages because the US government was able to tell consumers to not panic buy any meat products. JBS Foods unfortunately did have to pay $11 million in ransom even after consulting with digital security experts about the situation. It is now one of the largest ransomware payments of all time.
Acer - $50 Million in Ransom
Acer is a Taiwanese computer and electronic manufacturer that was also attacked by the infamous russian group, REvil. The hackers were able to find a vulnerability in the Microsoft Exchange’s servers. This gave them access to Acer’s data that included images of sensitive financial documents, bank balances, and bank communication. REvil demanded $50 million in ransom with this attack. Acer did come back with an offer of $10 million but the hackers rejected. Acer has still made it unclear if they paid the ransom or not.
Colonial Pipeline - $4.4 Million in Ransom
The Colonial Pipeline obtains about 45% of the East Coast’s supply of jet fuel, diesel and petroleum. In May, 100 GB of data was hacked by an organization called the DarkSide and they threatened to release this information until they were paid a ransom, forcing them to pay $4.4 million in bitcoin. This also resulted in gas prices rising up to 6 cents in the U. causing many people to panic buy, creating fuel shortages and disruption of the supply. Fortunately, US law enforcement was able to recover most of the ransom paid.
Kaseya - $70 Million in Ransom
Kaseya, also known as an IT management software company for MSPs and internal IT organizations, was also attacked by the russian hacker group, REvil. The hackers were able to take control of Kaseya's Virtual System Administrator and send out fake software updates to their direct clients and customers. REvil was able to encrypt one million systems and held these for a ransom of $70 million in bitcoin. According to Kaseya, about 50 clients and almost 1,000 businesses were impacted by this breach.
The FBI was able to get into REvil’s servers and undo the encryption to stop the attack. DNSFilter also made a statement on the attack and is also mentioned in the 2021 Domain Threat Report here. Even though Kaseya did not have to pay the ransom and was able to restore access to their servers, this will be one of the biggest ransomware attacks of the year—and likely years to come.
Don’t become another statistic
Want to know the best way to protect your organization from these malicious attacks? A layered approach that includes DNS security can help protect you from over 33% of attacks. Don’t end up on this list next year and start your free trial of DNS Filter today.
Having trouble deciding which protective DNS provider would be best for your organization? We’ve got you covered! Download our new 2021 Benchmark Report today.
 The AI Tools Your DNS Can't See
The AI Tools Your DNS Can't See
CyberSight's new AI Usage Report sees what DNS misses: Locally installed AI clients, locally-hosted models, and the active time employees spend in each.
 DNSFilter and Pax8: A Platinum Partnership Heads to Beyond
DNSFilter and Pax8: A Platinum Partnership Heads to Beyond
The relationship between DNSFilter and Pax8 just got stronger. We're proud to announce that DNSFilter has reached Platinum partner status with Pax8 and we're heading to Pax8 Beyond as a Gold Sponsor June 7-9.
 DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
Strengthening the global fight against cybercrime through shared intelligence and cross-sector collaboration
