On the NSA and CISA’s Latest Protective DNS Selection Recommendations
by Jen Ayers on Mar 19, 2021 12:00:00 AM
Written by Jen Ayers in collaboration with Jillian Kossman.
Recently, the NSA (National Security Agency) and CISA (Cybersecurity and Infrastructure Security Agency) published a guide to Protective DNS Service (PDNS). This is not the first time in 2021 alone that the NSA has made a recommendation related to enterprise-grade DNS. Strong endorsements for a DNS-focused security layer from government agencies are leading indicators of broader trends, For both public and private entities, looking to create a barrier between employees and malicious sites using DNS protection is becoming a standard.
In this blog we break down the key points made in their guide to Selecting a DNS Agency.
Key Capabilities
The NSA/CISA list of providers includes only providers which currently provide DNS filtering and PDNS services to large government entities. It did not assess actual performance, nor did it consider multiple providers that do not work with government agencies. Below is a breakdown of how DNSFilter meets the requirements of the NSA/CISA’s feature list.
| Features | DNSFilter |
|---|---|
| Blocks malware domains | |
| Blocks phishing domains | |
| Malware Domain Generation Algorithm (DGA) protection | |
| Leverages machine learning or other heuristics to augment threat feeds | |
| Content filtering | |
| Supports API access for SIEM integration or custom analytics | |
| Web interface dashboard | |
| Validates DNSSEC | |
| DoH/DoT capable |
Why Protective DNS (PDNS) matters
As with many Internet protocols, DNS was not built to withstand abuse from bad actors intent on causing harm. “Protective DNS” (PDNS) is different from earlier security-related changes to DNS in that it is envisioned as a security service – not a protocol.
DNSFilter was founded on the idea that domain protection is, and should always be, a key part of a multi-layer security strategy. More than 60,000 phishing websites were reported in March 2020, and the number of phishing attacks has doubled year over year since the early 2000’s.
New NSA & CISA Guidance
Due to the centrality of DNS for cybersecurity, the Department of Defense (DoD) included DNS filtering as a requirement in its Cybersecurity Maturity Model Certification (CMMC) standard (SC.3.192).
This is big. The Department of Defense is adding DNS filtering to its security standards. It currently appears as a prerequisite for Maturity Level 3. Based on the growth of malicious websites, we expect PDNS to become a standard across all security levels for government entities, and an expectation for enterprise organizations who want to protect against cyber attacks. Any company seeking to do business with the DoD, or any government agency, are held accountable to high security standards. They need to be prepared to add DNS protection to their stack in order to comply.
On Domain Categorization
The resolver usually checks both the domain name queries and the returned IP addresses against threat intelligence, and then prevents connections to known or suspected malicious sites. For example, these may include sites hosting malicious JavaScript®2 files or domains that host advertisements that collect information for undesired profiling. PDNS can block and alert on known malicious connection attempts
Checking against a static list of malicious domains and IP addresses identified by threat intelligence misses a huge portion of attacks: zero-day threats. Zero-day threats are system penetrations in which the hacker exploits a weakness that the company/engineers don’t yet know about. The 2014 Sony data breach is a famous example of a zero-day data breach. In the context of DNS security and DNS filtering, a zero-day threat is a threat that takes advantage of a domain that has not yet been categorized (or re-categorized) as containing malware or ransomware. These sites may be new, but they also may be previously benign sites that have been purchased or taken over by malicious actors.
DNSFilter’s AI continuously scans sites for potentially dangerous domains, giving us a greater ability to defend our customers from zero-day threats. We typically identify domains as malicious up to 80 hours before traditional threat feeds.
On Phishing
Threat actors lace phishing emails with malicious links
Most successful cyber attacks and serious data breaches come from human error. Often this human error is clicking a link in a phishing email. 94% of malware is delivered via email, and the average cost of a ransomware attack to a business is $133,000. User training is essential in helping your employees identify phishing and spear phishing attacks, but tools such as DNSFilter provide security by scanning domains in real-time using AI. This means malware can be blocked even if an unsuspecting user clicks a link in a phishing attempt.
On Typosquatting
Protecting users’ DNS queries is a key defense because cyber threat actors use domain names across the network exploitation lifecycle: users frequently mistype domain names while attempting to navigate to a known-good website and unintentionally go to a malicious one instead.
It has become standard practice for large entities to purchase domain names that are similar to their actual brand.com. Amazon owns Amzon.com, Amazan.com, and Amzn.com, among other domains to protect from typosquatting. If they did not, a hacker could use one of these typos, all of which receive 1,000s of search queries a month, to serve up malware, ransomware, or a tracking widget.
But you can’t rely on big brands to register every possible typo of their domain.
Reporting & Logging
Additionally, PDNS providers may collect and store the logs of DNS queries or provide them to the organization for it to keep. In either scenario, historical DNS logs can prove useful for retroactively searching for indications of earlier intrusions using indicators that only become known later on.

Keeping records of DNS queries is crucial. While our DNSFilter customers have access to their query logs for up to 90 days, we have longer-term access to those files. This allows us to check for abnormalities and impacted parties when new malware is discovered so we can alert our customers.
Other Considerations For Selecting a PDNS Provider
Using a PDNS provider as part of your overall security strategy is likely to become the standard for enterprise organizations, government agencies, educational institutions, and other businesses that are at a high risk for network security attacks.
Ease of deployment is crucial. Your organization will likely need to roll out a solution swiftly, and will want a PDNS tool that can be implemented within your timeframe. Solutions that aren’t solely focused on providing protective DNS are going to require a longer time to stand up. With a lightweight, yet powerful, tool like DNSFilter, you can simply point your network to our resolvers and be set up in a few hours.
Roaming Clients are essential, especially in a work-from-home environment where users are no longer protected by the company network. These users might be using personal devices that have no security software installed—putting your company at risk. A product like DNSFilter offers protection for any operating system with a variety of deployment methods depending on what makes the most sense for your business. DNSFilter provides that critical, first layer of protection no matter what device your employee is using.
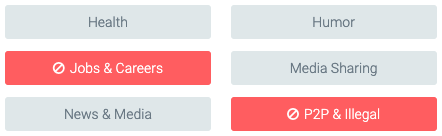
Content filtering capabilities are an added benefit of a PDNS service. They allow your organization to block inappropriate content such as pornography, social media, gambling sites, etc. And you can implement this content filtering through an unlimited number of policies to give you control over who sees what content based on role, department, campus, or any other factors.
DNSFilter provides the flexibility that enterprises demand backed by a fully redundant and reliable network to power DNS filtering and DNS threat protection.

 DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
Strengthening the global fight against cybercrime through shared intelligence and cross-sector collaboration
 CyberSight Gets Sharper: Threat Trends and Timeline Now Available
CyberSight Gets Sharper: Threat Trends and Timeline Now Available
When we launched CyberSight in March, the goal was clear: close the visibility gap between what DNS logs show and what users actually do. Activity logs, full URL tracking, application usage, device state—the data security teams need but haven't had from their DNS provider.
 We've Gone to the Dark (Mode) Side
We've Gone to the Dark (Mode) Side
A long time ago, in a dashboard far, far away...your eyes were suffering.
We know. We've heard about it since 2019: 270 of you voted for Dark Mode on our feature request board. Some of you left comments. One of you simply wrote: "So much white... Need dark mode please!" Honestly? Fair.
