DNSFilter Ranks #1 in G2’s Fall 2022 Reports
by Jenine Laviola on Oct 4, 2022 12:00:00 AM
Recently it was announced that DNSFilter is ranked #1 in 15 reports by G2, the world’s largest and most-trusted software marketplace.
This recognition is based on the responses of real users for each of the related questions featured in the G2 review form.
Some standout G2 reports include:
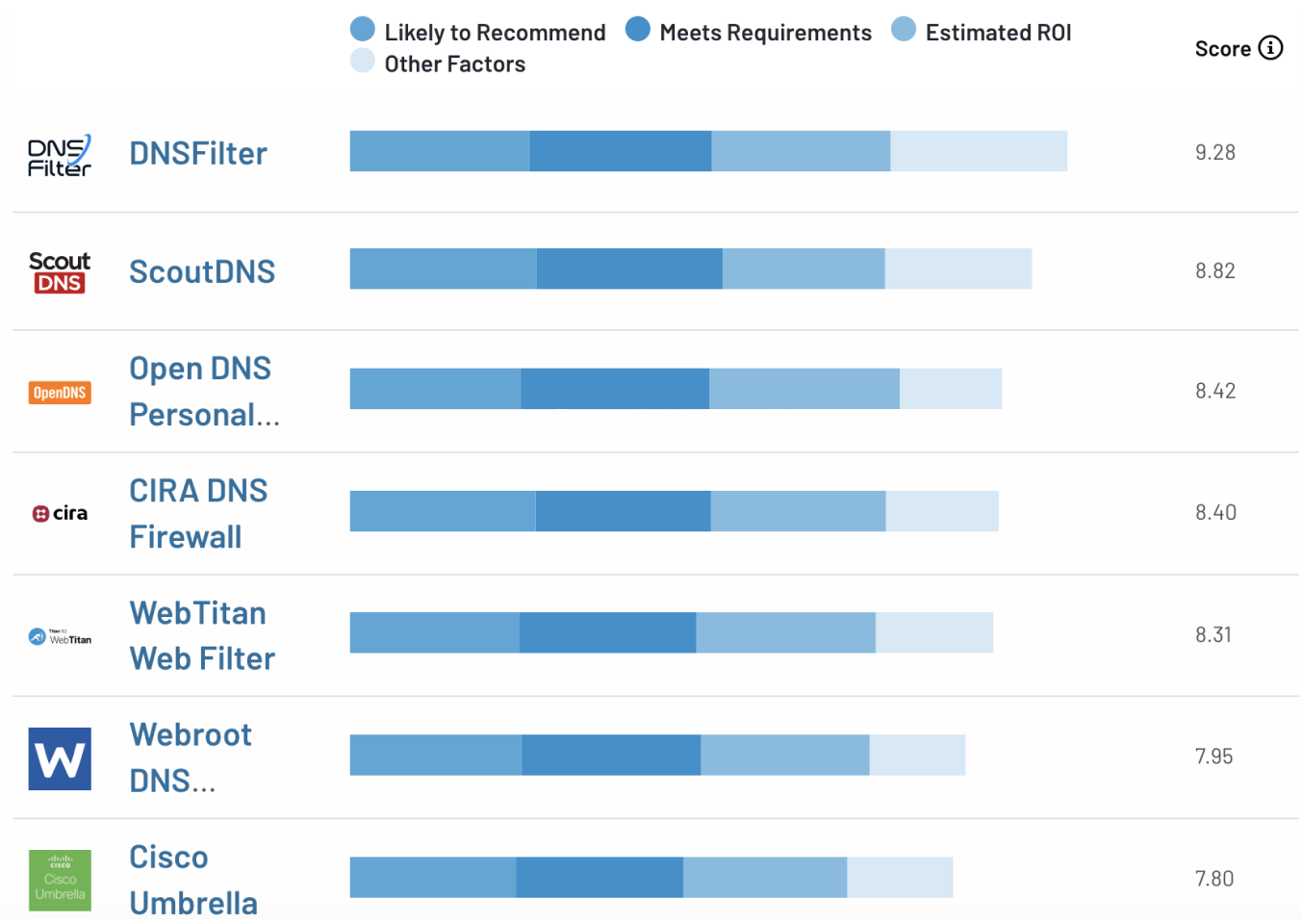
#1 in Results For DNS Security
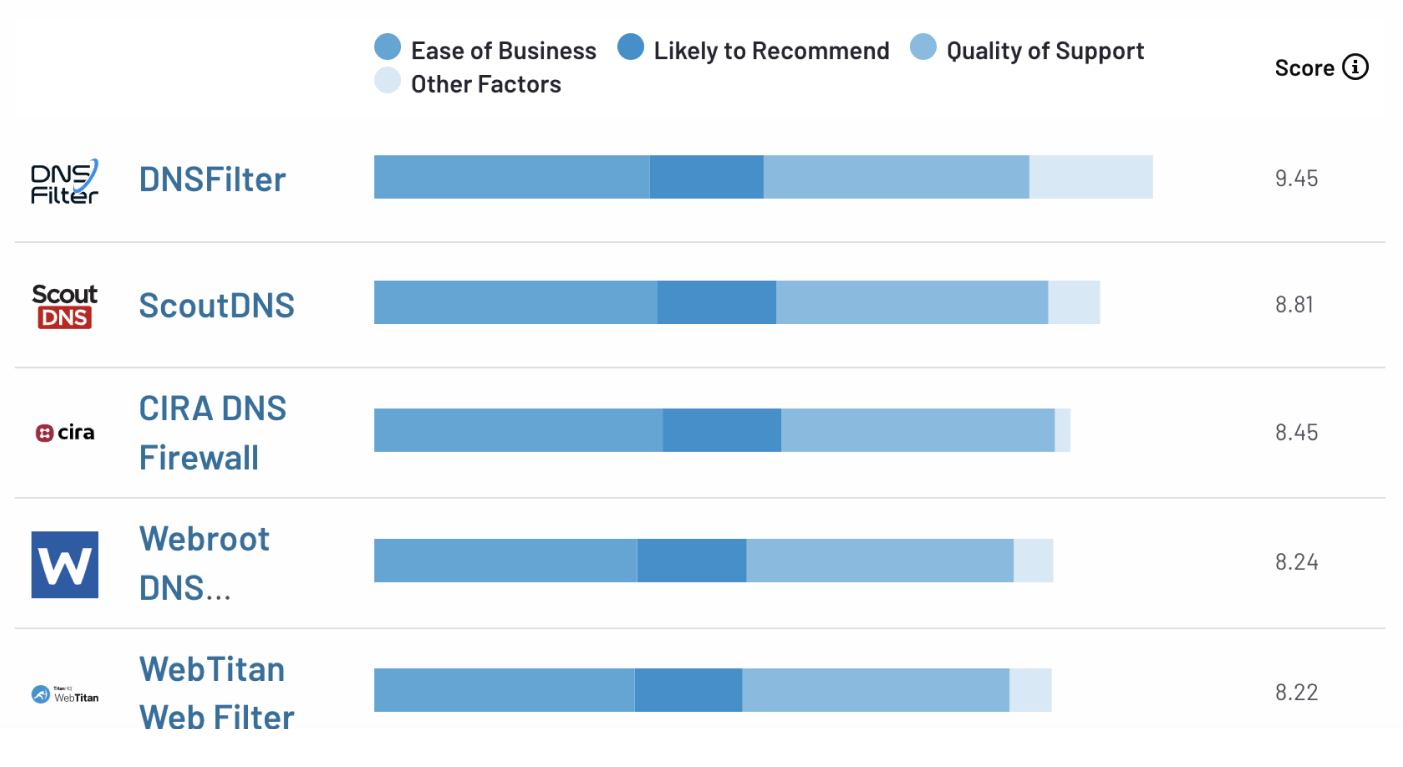
#1 in Relationship For DNS Security
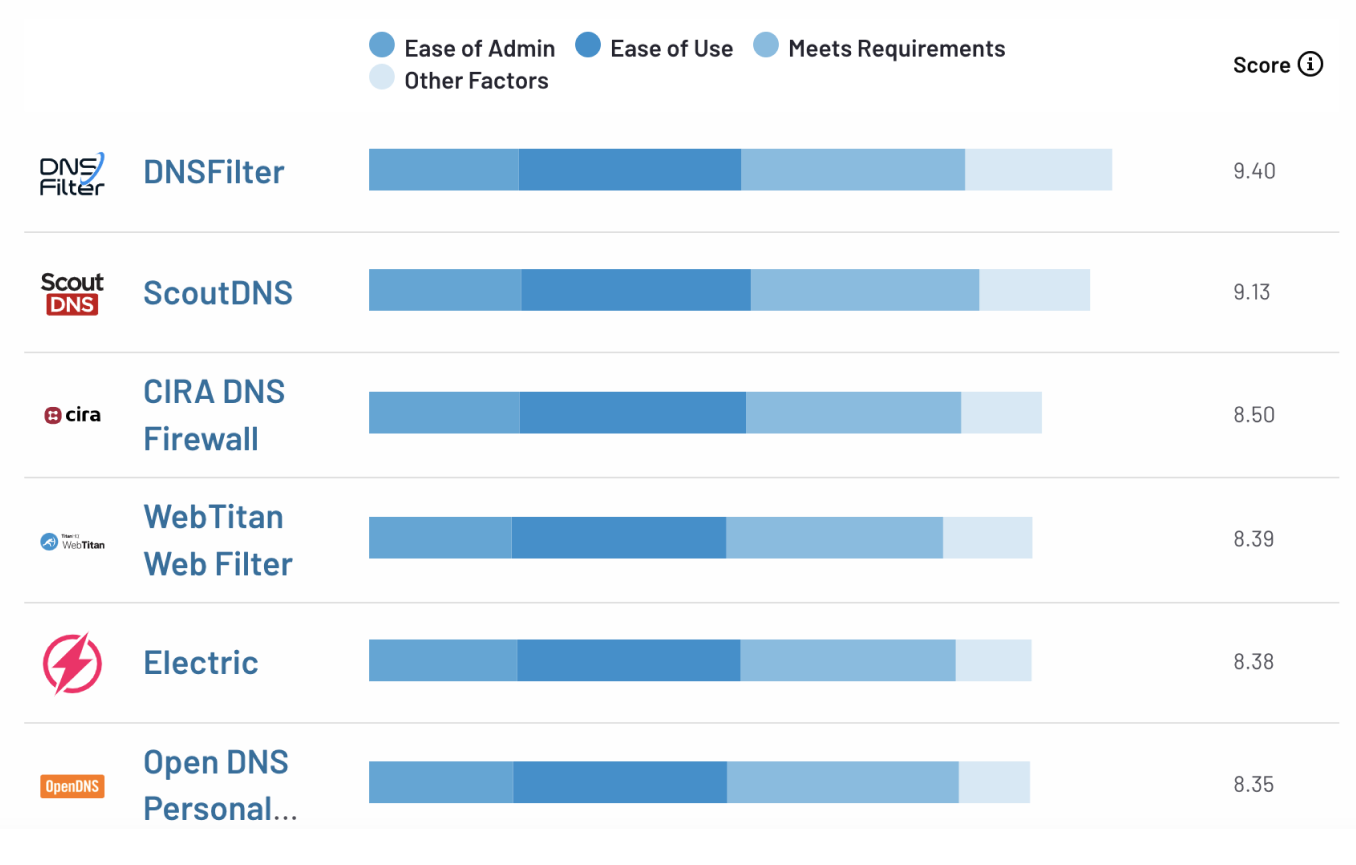
#1 in Usability For DNS Security
Each report is based on ratings by business professionals. DNSFilter received 10 or more reviews and five responses for each category-related question to qualify for inclusion in each report type.
“Rankings on G2 reports are based on data provided to us by real software buyers,” said Sara Rossio, Chief Product Officer at G2. “Potential buyers know they can trust these insights when researching and selecting software because they’re rooted in vetted, verified, and authentic reviews.”
Here are some of our latest reviews:
“All our endpoints are not affected by any latency issues since DNSFilter offers cloud-oriented DNS protection to our application sites. We make use of its web filtering options to enhance our user security while they access diverse websites. We can also establish its installation in any instance with ease & build multiple pseudo ACL policies based on customer preferences.”
- Mohana R. -Senior Software Engineer
“We are a small MSP and DNSFilter is a core part of our Cyber security offering. Setting it up only takes a few minutes and BAM!! All the bad traffic is immediately filtered out. Reports show the stuff that's blocked. From there we're able to see bad traffic and take action from there. If something needs to be whitelisted, it's fast and easy. Mobile devices outside of the office network are easy to manage. Their MSP billing model is inexpensive, scalable, with no commitment.”
- Joe C. - Owner
DNSFilter continues to be a proven leader in DNS Security Software, beating out those with similar products. In fact, DNSFilter has now been awarded 63 G2 Badges 9 quarters in a row!
Want to help us keep celebrating? Write us a review here.
 The AI Tools Your DNS Can't See
The AI Tools Your DNS Can't See
CyberSight's new AI Usage Report sees what DNS misses: Locally installed AI clients, locally-hosted models, and the active time employees spend in each.
 DNSFilter and Pax8: A Platinum Partnership Heads to Beyond
DNSFilter and Pax8: A Platinum Partnership Heads to Beyond
The relationship between DNSFilter and Pax8 just got stronger. We're proud to announce that DNSFilter has reached Platinum partner status with Pax8 and we're heading to Pax8 Beyond as a Gold Sponsor June 7-9.
 DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
Strengthening the global fight against cybercrime through shared intelligence and cross-sector collaboration
