DNSFilter at Black Hat USA: Guardian Acquisition, Reducing Risk, Nation-State Attacks
by Serena Raymond on Aug 15, 2022 12:00:00 AM
For the DNSFilter team, Black Hat was really just two days on the ground. Two busy, jam-packed, amazing days filled with dozens of sessions, lots of time at the booth and walking the business hall, and hundreds of conversations with security professionals from around the globe (111 different countries, to be exact). But still, it was just two days for the team of 16 we brought to Black Hat to absorb all we could before packing it up and heading home.
Though it was a whirlwind, we came away with some great insights we’ll certainly be applying, and we also want to share what we’ve learned.
Here are a few interesting takeaways and big announcements from Black Hat USA 2022.
Risk reduction is on everyone’s minds, but erasing risk completely is impossible
Prior to Chris Krebs taking the stage at the opening keynote for the week, Jess Moss (founder of Black Hat and CEO & founder of DEF CON Hackers) said that had you asked him 25 years ago he would have assumed that security would have been “mostly baked” by 2022. But here we are, still trying to figure it all out.

Moss recalled the original goal of the Black Hat conference (“briefings of what the Black Hats are up to”) and some of the actions taken by the conference to get organizations and consumers to care more about security. First, they published a guide to secure products—it didn’t quite work. Then it was about online protection: Educating companies on how to be online securely. That didn’t quite work either. Finally, they saw an opportunity for regulation around security.
But we’re still struggling to secure everything, aren’t we? And a huge factor in security is mitigating risk.
There were a few sessions that dealt specifically with reducing risk, and they really all had the same conclusion: It is impossible to reach 100% risk reduction. And while we’d all love for a “one weird trick” solution to this problem, the reality is we need to focus less on how to remove actions that are risky and more on how to make risky actions safer.
Kyle Tobener, VP, Head of Security & IT at Copado gave a presentation entitled “Harm Reduction: A Framework for Effective & Compassionate Security Guidance.” He gave the example of how e-cigarettes were initially treated in the US vs. the UK. In the US, e-cigarettes were banned while in the UK they were regulated. The US had more deaths related to e-cigarettes, and children and teenagers were targeted by advertisers. In the UK, there were no deaths.
But what’s missing in a lot of these scenarios is the “why.”
We need to educate, explain why something is not accessible on the network, or why a certain application is risky. We can give the reasons why, and then also provide safer alternatives. Kyle gave the example of accessing TikTok in a web browser instead of via the app on your phone.

Small changes can make a big impact. And we can adopt this mentality when interacting with customers and employees—but we need to be compassionate.
Have you heard of “Nation-State Attacks”?
Hopefully it’s clear this question was rhetorical.
Nation-state attacks have been absorbing our attention for the majority of 2022 (and let’s be honest, even before that). Just two weeks before Black Hat, we were writing about how to spot nation-state attacks.
Therefore, it shouldn’t be a shock that these attacks were referenced repeatedly throughout sessions—not to mention, according to a talk I’ll discuss in the next section, there was at least one attack on Black Hat itself that had that nation-state flavor.
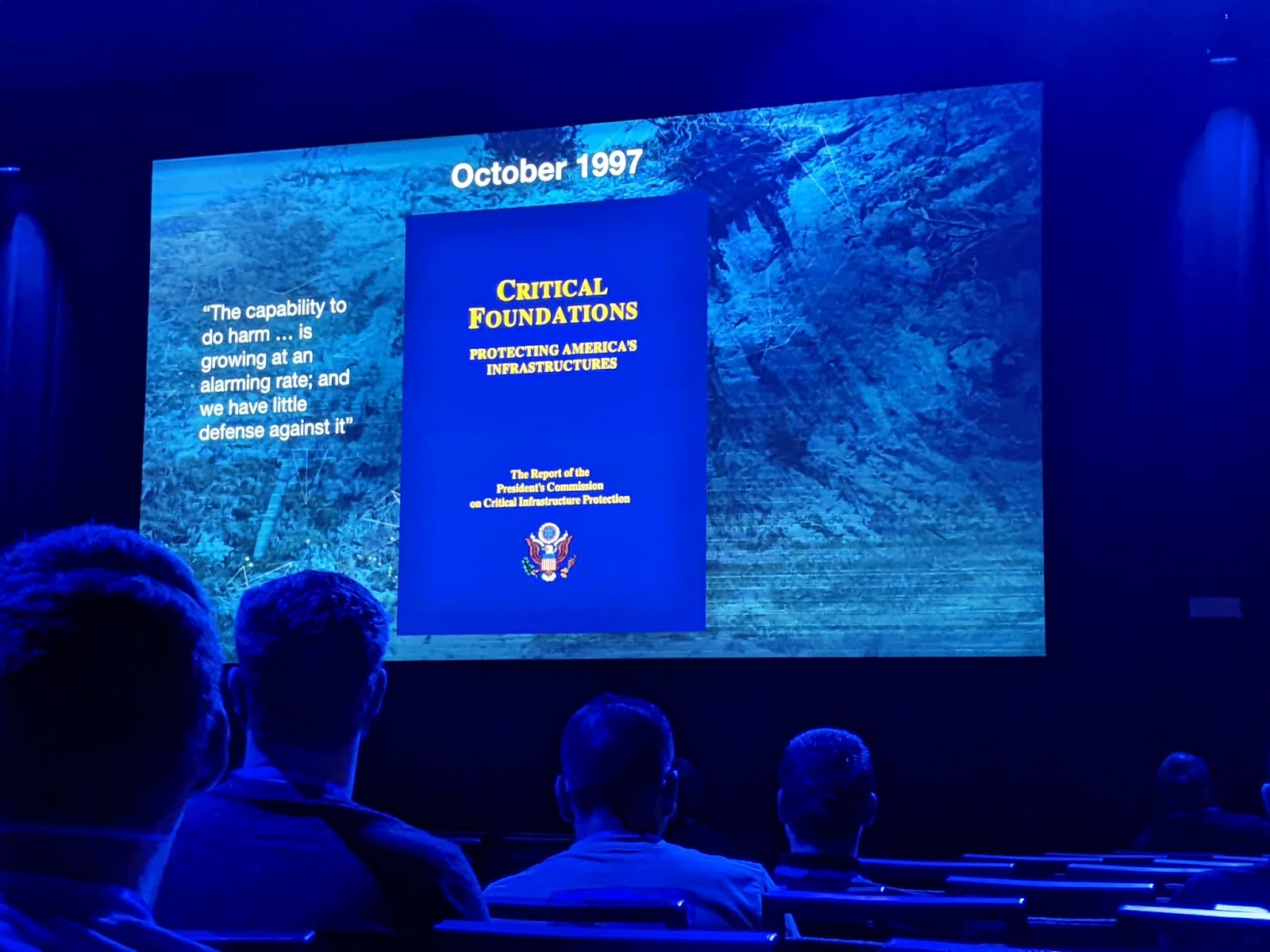
The keynote by Kim Zetter to kick off Day 2 dwelled on “digital war,” for good reason. Despite having a clear need for ransomware response and mitigation programs for over 20 years, many organizations (and especially those that comprise our critical infrastructure) are lagging behind. And that is making us far more vulnerable to nation-state attacks. Though, it’s been this way for quite some time.
Zetter’s talk focused heavily on Operation Aurora and the computer worm Stuxnet.
The main events discussed both took place in 2010 (with Stuxnet occurring second, though believed to have been deployed as early as 2005).Of course, versions of Stuxnet are still around today.
Operation Aurora was a China-based cyberattack that targeted private companies in the US, with Google being the primary target. While Stuxnet is often regarded as the first intentional act of cyberwarfare (possibly built jointly by the US and Israel), it had the ability to spy on users after being deployed. Stuxnet caused significant damage to Iran’s nuclear program.
“They [Operation Aurora and Stuxnet] fundamentally shifted the performance landscape by shattering old mindsets and stimulating new ideas for highly targeted attacks with far-reaching consequences,” Jeffrey Carr wrote for Forbes back in December 2010.
None of this is new. But recent events in Ukraine, Russia, and Iran (where gas pumps were shut off) signal a possible rise in these types of attacks that we all need to be vigilant about.
Identifying and tracking possible nation-state malware is an increasingly necessary function that all security practitioners need to take part in.
Telling NOC NOC jokes
One of the more fascinating sessions at Black Hat (for all you network security nerds) was “The 8th Annual Black Hat USA NOC Report” by Grifter and Bart Stump.
Black Hat is really at its best when it goes completely meta. Yes, Black Hat is the hacker conference. Security concerns are rampant. Malicious exploits and attacks on registration are everywhere—so how do those responsible for the network secure it?
In this talk, we found out how. The leaders of the Black Hat NOC take a layered security approach. They laid out their entire hardware setup (gave a brief overview of how things used to be secured “in the old days”), the software they use (including DNS security, firewalls, and plenty of visualization tools!), and discussed some of the wildest things they’ve seen at Black Hat this year.

When they pulled the reports mid-day on Day 2 (right before this presentation), they had seen over 93,000 DNS requests identified as malware across over 10,000 devices.
The only thing the Black Hat NOC doesn’t do is encrypt. When they see something they can verify to be malicious, they will shut it down. They’ll reach out individually to those who seem to be targeted (usually via captive portal, though back in the day they used to knock on classroom doors). And while the NOC is also a SOC, their primary goals are related to building and maintaining the network’s reliability above all else.
As they put it, they replace everything except for the wires in the walls.
They encountered many messages being sent in the clear—including some sensitive financial transactions using an application that sent APIs in clear text.
The takeaway here is that we can only trust the applications we use to a point. We expect that they are doing things securely, but we can’t take it for granted. Applying our own layers of security over top of these risky applications is absolutely paramount.
DNSFilter acquires Guardian—extending future features for our customers
We made our own very important announcement on the first day of Black Hat. We acquired the leading cloud firewall + VPN technology company, Guardian.

Over the coming months, DNSFilter will begin to integrate Guardian’s technology into DNSFilter to implement IP, URL, and file type filtering in 2023. Protective DNS is a vital element of Secure Web Gateway (SWG), and our acquisition of Guardian will enable us to apply best-in-class capabilities to a space that is currently composed of legacy technology.
Read more about the acquisition of Guardian here.
Interested in discovering how DNSFilter fits into your security stack? Request a demo today.
 DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
Strengthening the global fight against cybercrime through shared intelligence and cross-sector collaboration
 CyberSight Gets Sharper: Threat Trends and Timeline Now Available
CyberSight Gets Sharper: Threat Trends and Timeline Now Available
When we launched CyberSight in March, the goal was clear: close the visibility gap between what DNS logs show and what users actually do. Activity logs, full URL tracking, application usage, device state—the data security teams need but haven't had from their DNS provider.
 We've Gone to the Dark (Mode) Side
We've Gone to the Dark (Mode) Side
A long time ago, in a dashboard far, far away...your eyes were suffering.
We know. We've heard about it since 2019: 270 of you voted for Dark Mode on our feature request board. Some of you left comments. One of you simply wrote: "So much white... Need dark mode please!" Honestly? Fair.
