The Downside of Public Wi-Fi
by Lola Dominguez on Aug 18, 2022 12:00:00 AM
Public Wi-Fi hotspots have increased in number over time as the demand for accessibility is a part of daily life. No more are the days of having to access Wi-Fi at the library or coffee shops–Wi-Fi is accessible everywhere from restaurants, barber shops, airports, and even cruise ships. But is it secure?
How Secure is Public Wi-Fi?
In 2021, DNSFilter conducted an internal project to test what kind of content is accessible on public Wi-Fi. While traveling to attend our annual company retreat, employees set out to do an informal experiment: How secure is airport Wi-Fi?
In an attempt to find the answer, the DNSFilter team tested 1,249 domains across U.S. airports.
Putting Airport Wi-Fi to the Test
The content on these domains contained any of the following content: Weapons, adult content, botnet, gambling, malware, drugs, illegal peer-to-peer, phishing, and terrorism/hate. The test marked if the domains were allowed, blocked, or unresolved.
If the domain accessibility was marked “unresolved”, this meant that the site was not accessed, but it was not blocked either. One would assume that these domains would all be blocked from public access, particularly airports, but to our surprise, most of the content was not blocked.
Results are as displayed below:
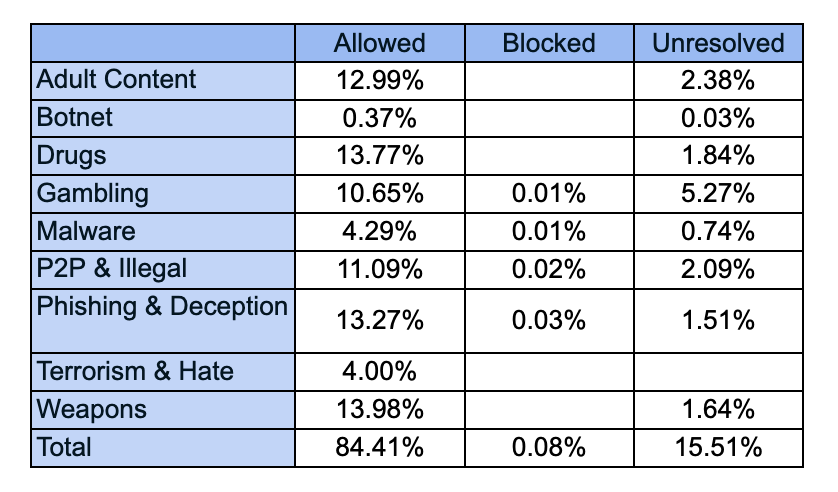
Overall, a whopping 84% of the domains tested were accessible on public Wi-Fi. Content that was blocked were gambling, malware, peer-to-peer, and phishing. Unsurprisingly, gambling content was blocked at airports located in states where online gambling is prohibited.
Constant Connection has Consequences
It might be a surprise to find that the domains DNSFilter tested were easily accessible on airport public Wi-Fi, but the results paint a picture of how the convenience of always being connected can have consequences.
One data point that seems to stand out is that sites containing weaponry content, and also terrorism/hate content, were allowed on airport Wi-Fi. Generally, airports are associated with strict security and watchful eyes observing for behavior that could pose a threat, so it does come as a surprise that the results show less strict rules on public Wi-Fi.
In addition, malware, phishing, botnet, and illegal peer-to-peer content were not blocked in most cases. Spotting this type of content is not always apparent to individuals, so not having a protective layer in place to filter out this content on public Wi-Fi puts everyone on the network at risk.
Even adult content was not blocked in most cases. Imagine: You finally made it through the long line at the TSA checkpoint after being questioned about your liquid toiletries and shuffling to put your shoes back on. You have a moment to spare before your flight, so you sit down in the only chair available near your gate and the person next to you is logged into an adult site. This would be an extremely uncomfortable situation for you, and for others around you.
Public Wi-Fi is Never Fully Secure
It is a great luxury to have access to Wi-Fi at all times. We can communicate more frequently than we did 20 years ago and we can conduct business from anywhere in the world. Think about all the times you have been in the waiting room for a doctor’s appointment so you pass the time on social media, or when your internet connection goes out at home so you run to the nearest Starbucks to plug in.
Did the risks of being on public Wi-Fi even cross your mind before connecting?
In an ideal world, no one should have to think about these risks, but unfortunately there are some threats to safety when using shared public Wi-Fi. The lesson here: Public Wi-Fi is never fully secure.
Use Public Wi-Fi Safely
There are a few precautions that can be taken when using public Wi-Fi:
- Protect your data by encrypting it. Consider using a VPN app which encrypts your data while you are using a public network. VPNs can also protect your location.
- Never access your personal financial information using public Wi-Fi. Only log into sites that are encrypted. If you must access personal information, using your mobile data is more secure than using public Wi-Fi, as mobile data is usually encrypted.
- Pay attention to warnings that sites send you. If you try to access a site that gives a warning, it is best not to continue to access that site.
- Inspect the URL of the site you are trying to access. Phishing sites resemble popular sites but will have a slight variation in spelling. Oftentimes these variations are not noticeable unless you slow down to read it.
- Do not download apps or files while on a public network. For parents who bring tablets to entertain their children while out in public, it is best to not connect these devices to the public Wi-Fi. Download any games or movies at home before leaving the house. There are also parental control apps available that can be used to control what your child can access on their devices.
Overall, the availability of connectivity in public is more beneficial than it is risky. However, being educated on the dangers of public Wi-Fi and how these can be avoided goes a long way for your safety and that of others. Next time you ask your server at a restaurant for the Wi-Fi password, take a second to consider whether the ability to scroll on Facebook is worth the risk.
For more information about public Wi-Fi safety and harmful content, find these additional resources:
How to Safely Use Public Wi-Fi Networks
How to Spot a Phishing Website
 The AI Tools Your DNS Can't See
The AI Tools Your DNS Can't See
CyberSight's new AI Usage Report sees what DNS misses: Locally installed AI clients, locally-hosted models, and the active time employees spend in each.
 DNSFilter and Pax8: A Platinum Partnership Heads to Beyond
DNSFilter and Pax8: A Platinum Partnership Heads to Beyond
The relationship between DNSFilter and Pax8 just got stronger. We're proud to announce that DNSFilter has reached Platinum partner status with Pax8 and we're heading to Pax8 Beyond as a Gold Sponsor June 7-9.
 DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
DNSFilter Joins the World Economic Forum-hosted Cybercrime Atlas as a Community Member
Strengthening the global fight against cybercrime through shared intelligence and cross-sector collaboration
